News
Zeus Panda Malware can Clean out your Bank Account!
a text message, it is being delivered right through an internet search! How it works: Hackers create multiple malicious websites that show up at the top of the search engines when you look for your bank. When you click on the one you think is correct, you are...
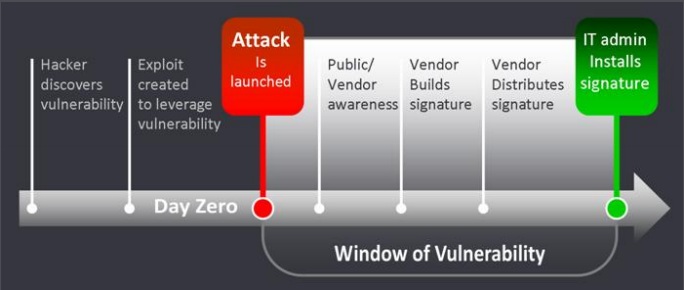
Cyberattacks – Part 10: Zero-Day Exploits
Zero-Day Exploits refers to a vulnerability in software that hackers have found and before the software company finds it and comes up with patch to fix it. This is not rare. Hackers are smart, otherwise they wouldn’t make money! A lot of the time software developers...

Cyberattacks – Part 9: Ransomware
Ransomware is any software that encrypts your data until a sum of money is paid. There are a few different ways ransomware gets installed: 1: Drive by downloads 2: Clicking on an attachment in an email 3: Websites with Trojans that you may come across accidentally How...

Cyberattacks – Part 8: Viruses
Viruses are malware, or malicious software, that spreads through your computer and multiplies as it goes. They can slow your computer down, corrupt files, even corrupt the operating system, making it impossible to use your computer. While viruses, generally speaking,...

Cyberattacks – Part 7: Malware
Malware is a very broad term. Basically, it is software that is software that is created to damage your system and/or to get your personal information. A smaller section of malware is malvertisting. This is an ad online with code in it so when you click on the image...

Cyberattacks – Part 6: Pharming
This is a newer term than phishing but still one we have all heard. Pharming: While similar to phishing it is different. This is a where hackers make a convincing looking website or ad. After clicking on the website or ad they request your log in information and...

Cyberattacks – Part 5: Phishing
This is a term we have all heard but what does it mean? Phishing: This is an attempt, usually through the email, to get your information. The hackers set up an email that is supposed to look like it’s from someone you know. Signs of a phishing scam: 1: There are...

Cyberattacks – Part 4: Spoofing
Spoofing is when hackers manipulate the caller ID on your phone to make you believe that they are from one place when they really are just criminals trying to steal your information. Lately spoofers have been trying to call you from your own number! Here are a few...

Cyberattacks – Part 3
Drive by Downloads: This is the way that most malware is installed, accidentally. Cybercriminals can hide their malware anywhere! It could be an ad, a link, a pop up, or anything. Keylogger: This malware logs every key stroke you make on your computer even...

Cyberattacks – Part 2: Data Breaches
The Equifax data breach was front page news while the Yahoo data breach didn’t get as much attention. Why is that? And what exactly is a data breach? A data breach is a hacker logging into a secure system and stealing information. In the case of Equifax this...
Get Started On Your Service
Contact us if you have any questions about repair or upgrades, or just stop on in to one of our stores… no appointment necessary!
